Browser extensions are a great way to enhance your browsing experience, but they can also pose significant security risks to an organization.
What are Browser Extensions? Browser extensions are small software programs that add functionality and features to web browsers. They are typically created using web technologies such as HTML, CSS, and JavaScript. These extensions can be installed and used within a web browser to customize the browsing experience, improve productivity, or add new capabilities.
Zero-Trust Browser Extension Protection
The Malicious Potential of Browser Extensions
Browser extensions have become an integral part of our online browsing, providing additional functionalities and customizations. However, this convenience comes with inherent risks, as some extensions can be malicious in nature. Privacy breaches, data theft, and system vulnerabilities are some of the notable concerns associated with malicious browser extensions.
Privacy Breaches
Malicious browser extensions may compromise user privacy by tracking online activities, collecting personal data, or even intercepting sensitive information. For example, a seemingly innocent browser extension designed to enhance online shopping experiences might secretly track user behavior, collecting information about their browsing habits and purchase history. This data can then be used for targeted advertising or sold to third parties without the user's consent.
Data Theft
Some malicious extensions are specifically designed to steal sensitive information such as login credentials, credit card details, or browsing history. For instance, a seemingly harmless productivity extension might secretly capture keystrokes, recording everything the user types, including passwords and other confidential information. This stolen data can be exploited for various illicit purposes, including identity theft, financial fraud, or unauthorized account access.
System Vulnerabilities
Certain browser extensions contain vulnerabilities that can be exploited by hackers to gain unauthorized access to users' devices. These vulnerabilities might be a result of poor coding practices or inadequate security measures during the development process. Once a malicious actor gains access to a user's device through a vulnerable extension, they can potentially install additional malware, compromise system security, or gain control over the user's sensitive data.
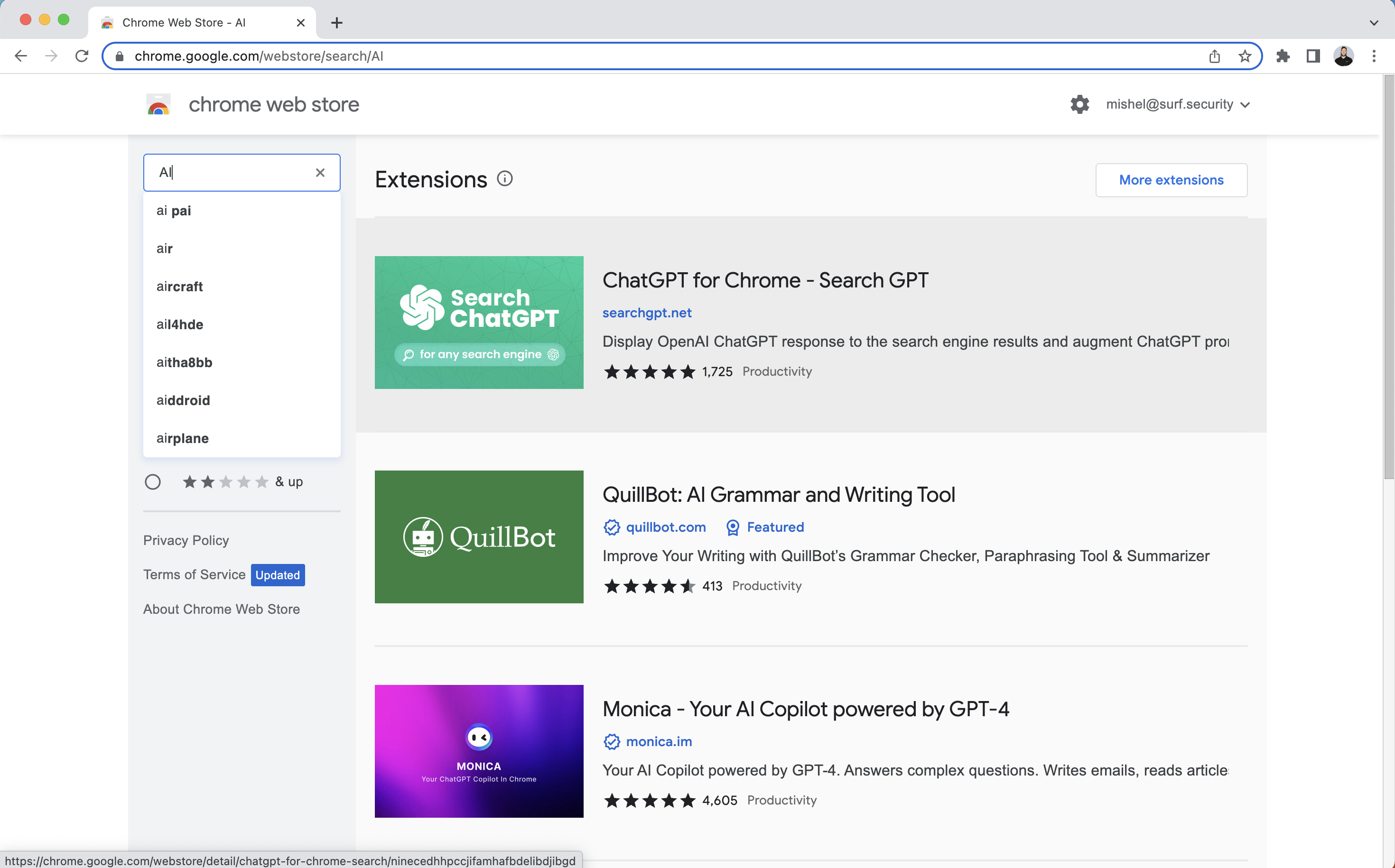
Risks of AI Extensions in the Modern Era
As AI continues to advance, AI-powered browser extensions have become increasingly prevalent. While these extensions offer innovative features and improved user experiences, they also introduce unique risks. Let's explore some of the specific challenges posed by AI extensions:
Access to User's Data
AI extensions often rely on vast amounts of user data for training their models, which raises ethical questions regarding data privacy, consent, and ownership. Users must be cautious about the information they provide to AI extensions and be aware of how their data is being used. For example, an AI-powered language translation extension might require access to the user's messages and emails to improve its translation capabilities. While this can enhance the user experience, it also raises concerns about the privacy and security of sensitive conversations.
Manipulation and Bias
AI algorithms powering extensions can unintentionally perpetuate biases or misinformation. If not carefully trained and monitored, AI extensions may inadvertently amplify existing societal prejudices or promote inaccurate information, potentially leading to detrimental effects on individuals and communities. For instance, an AI-powered news recommendation extension might prioritize articles that align with the user's existing beliefs, reinforcing their biases and limiting exposure to diverse perspectives.
Security Vulnerabilities
AI models within extensions can be vulnerable to adversarial attacks, where malicious actors manipulate the model's input to produce undesired or harmful outputs. One example of such an attack is prompt injection. Prompt injection attacks exploit the vulnerabilities in AI models by manipulating the input prompts given to the model. These attacks aim to deceive the model into generating biased or malicious outputs.
Imagine an AI-powered browser extension that provides automated content generation for social media posts. Malicious actors could manipulate the input prompt by injecting toxic or inflammatory language, leading to the generation of harmful and offensive posts. By exploiting prompt injection vulnerabilities, attackers can bypass any content filtering mechanisms.
The Zero Trust Enterprise Browser
The Zero Trust browser provides administrators with robust capabilities to manage extensions within the browser environment, allowing them to define what extensions are allowed and what extensions are not allowed based on the organization's security policies and requirements. Here's how the Zero Trust browser enables effective extension management:
Policy-Based Control: The Zero Trust browser allows administrators to define policies that govern the use of extensions. These policies can specify which extensions are permitted and which ones are blocked based on their security assessments. Administrators can create different policies for various user groups or departments within the organization, allowing flexibility in extension management based on necessity and security requirements.
Whitelisting and Blacklisting: Administrators can create whitelists and blacklists of extensions to manage their availability within the browser environment. Whitelisting allows only approved extensions to be installed and used, ensuring that users are limited to extensions that have undergone thorough security evaluations. Blacklisting, on the other hand, blocks known malicious or high-risk extensions, preventing users from installing or using them.
PII Masking: The Zero Trust browser provides the ability to mask personally identifiable information (PII) within web pages. This ensures that sensitive data such as names, addresses, social security numbers, or credit card details are not exposed to AI-based extensions. By masking PII, even if an extension attempts to analyze or extract information from the web page, it will only see masked or obfuscated data, protecting the privacy of users' personal information.
Input Obfuscation: The Zero Trust browser allows for the obfuscation of input fields that contain policy-sensitive information. When users enter sensitive data, such as passwords, credit card numbers, or other confidential information, the input fields are modified or randomized, making it difficult for AI-based extensions to interpret or understand the actual content. This ensures that sensitive information remains protected, even if extensions attempt to access or capture user input.
Centralized Management: The Zero Trust browser provides centralized management capabilities, allowing administrators to have full control over extensions across the organization. They can define and enforce extension policies, manage whitelists and blacklists, and monitor extension usage from a central console. This centralized approach streamlines the management process and ensures consistent security measures are applied to all users.
Automatic Malicious Extension Detection: The Zero Trust browser employs advanced threat intelligence and machine learning algorithms to automatically detect and block malicious extensions by design. It proactively scans extension repositories, analyzes extensions for potential security risks, and prevents the installation of known or suspected malicious extensions. This proactive approach helps protect the organization from potential threats posed by malicious extensions.
By providing powerful extension management capabilities, the Zero Trust browser empowers administrators to define and enforce extension policies, assess extension risks, and block malicious extensions by design. This proactive approach ensures that only trusted and secure extensions are allowed within the organization, reducing the likelihood of security breaches and maintaining a more secure browsing environment.