Do you know where your employees are inserting your company credentials? Do you know where they are uploading your corporate files and what they are downloading from your cloud storage?
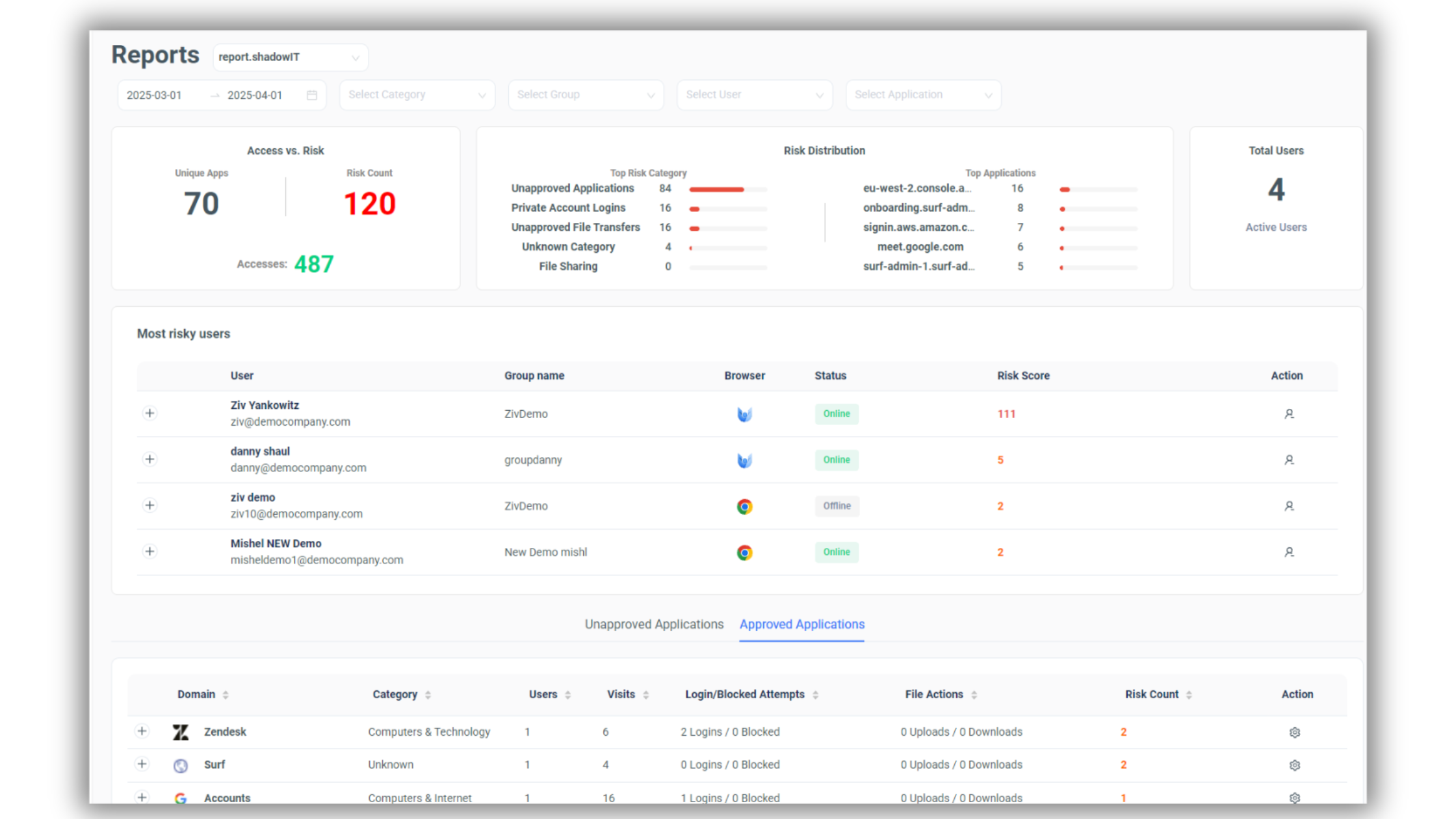
With the newly available Shadow IT Report from SURF, administrators can now gain full visibility into unsanctioned applications, unauthorized logins, and file-sharing activities. This powerful tool enables organizations to detect security risks, prevent data leaks, and ensure compliance with corporate policies. As a secured browser solution, SURF provides enhanced security for enterprise environments, ensuring safe and compliant browsing.
What Does the Shadow IT Report Provide?
SURF’s Shadow IT Report delivers deep insights into:
-
Unapproved Applications: Identify which applications your employees are accessing without approval.
-
Company Credential Logins: Detect when company credentials are used on non-corporate platforms.
-
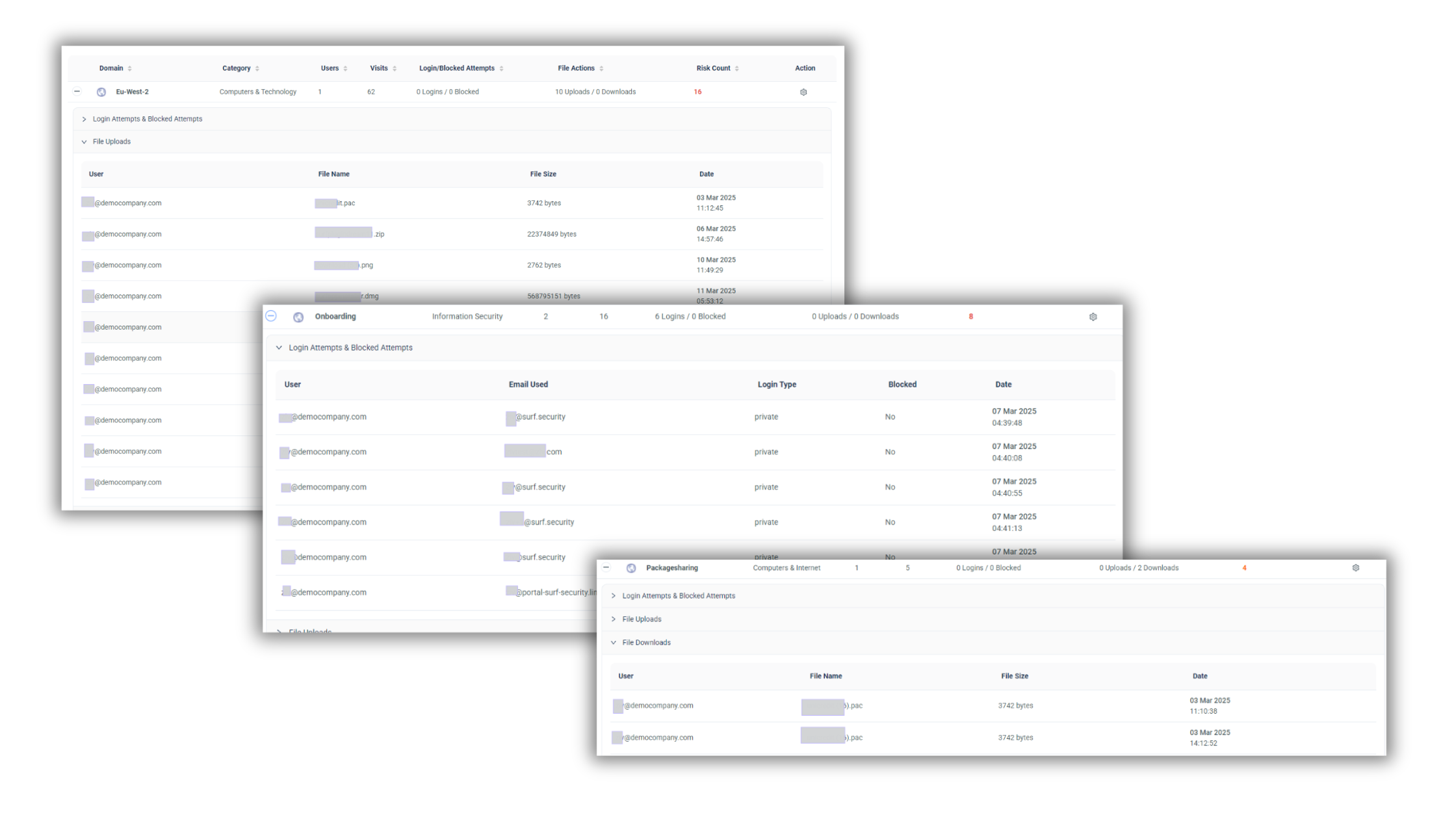
File Transfers & Downloads: Track file uploads and downloads from external sources.
-
Risk Scores & User Monitoring: Get real-time risk assessments for your employees based on their activity.
-
Browser Activity Insights: Identify which applications pose the highest risk to your organization.
-
Private Account Logins: Identify when personal credentials are being used within the work environment, helping to prevent security risks associated with unauthorized access.
How Does It Work?
By leveraging the SURF Enterprise Browser Extension and the SURF Enterprise Browser, administrators gain real-time data on employees' digital behavior. The Shadow IT Report consolidates this data into a detailed dashboard, providing a clear view of security threats, access patterns, and file-sharing trends.
Key Features:
-
A centralized risk dashboard displaying access vs. risk analysis.
-
A list of the most risky users based on login attempts and file activity.
-
Detailed event logs, including timestamps, application details, and associated risk levels.
-
Automated alerts for unauthorized logins and high-risk activity.
How SURF Prevention Controls Enhance Security
When combined with SURF Prevention Controls, the Shadow IT Report delivers an unmatched level of security oversight. Here’s how:
-
Proactive Threat Mitigation: Prevention controls allow IT teams to automatically block risky applications, preventing unauthorized access before a breach occurs.
-
Automated Remediation: If an employee attempts to log in to an unauthorized platform, SURF Prevention Controls can trigger immediate actions such as blocking the attempt or alerting administrators.
-
Granular Access Controls: Organizations can set custom access policies, restricting certain users or departments from accessing high-risk services.
-
Data Loss Prevention (DLP): By monitoring file uploads and downloads, SURF ensures that sensitive corporate data does not leave the company’s secure environment without authorization.
Why Is This Important?
With the rise of cloud-based applications and Gen AI security concerns, employees often bypass IT policies by using unauthorized tools. This increases the risk of data breaches, non-compliance, and exposure to cyber threats. The Shadow IT Report and SURF Prevention Controls empower administrators to:
-
Identify vulnerabilities before they become threats.
-
Enforce security policies effectively.
-
Enhance data security by monitoring file movements.
-
Ensure compliance with industry regulations.
-
Prevent unauthorized activity in real-time.
Take Control of Your Organization’s Security Today!
SURF’s Shadow IT Report, combined with Prevention Controls, provides unparalleled transparency and security control over your corporate environment. As a enterprise browser solution, SURF helps IT teams proactively address risks, secure corporate data, and maintain full control over their digital assets.
Get started today and gain full visibility into your company's IT landscape with SURF!
Scan the QR code for demo
